Why in the News?
A recent study testing 294 million domains across six major Internet Service Providers (ISPs) in 2025 reveals significant inconsistencies in website blocking. Despite receiving identical blocking orders, ISPs do not block the same domains. Out of 43,083 blocked domains, only 1,414 were uniformly blocked, highlighting a fragmented censorship regime. This is a major concern because it demonstrates that internet censorship in India is not centrally uniform but ISP-dependent, marking a shift from the assumption of standardised enforcement.
How does India’s legal framework enable internet censorship?
India’s legal framework enables internet censorship primarily through broad executive powers granted by the Information Technology Act of 2000 (IT Act), supported by constitutional, penal, and procedural regulations that prioritize national security and public order.
- Information Technology Act, 2000 (ITA): The IT Act is the primary legislation used for digital censorship.
- Section 69A: Empowered by the 2008 amendment, this section allows the central government to issue directives to block public access to any information online. Grounds include the interest of sovereignty, integrity, defense of India, security of the state, or public order.
- IT Blocking Rules, 2009: These govern the process of Section 69A, allowing for confidential takedown orders, which often lack transparency, limiting the ability of content creators to challenge them.
- Section 79 (3)(b): This section dictates that “intermediaries” (like ISPs, search engines, and social media sites) must remove content upon receiving “actual knowledge” or being notified by the government that their platform is being used for unlawful acts. Failure to comply can lead to a loss of “safe harbor” protection, making them liable for user content.
- IT (Intermediary Guidelines and Digital Media Ethics Code) Rules, 2021: These rules significantly tightened control over online content.
- Content Takedown Timelines: Intermediaries must remove “unlawful” content within set timeframes (often within 36 hours, but tighter for specific content) after receiving a complaint or government notice.
- Mandatory Grievance Redressal: Platforms must establish an internal mechanism to handle complaints, strengthening the government’s ability to demand removal.
- Expedited Removal for Specific Content: Recent amendments (as of 2026) have proposed removing content within as little as three hours.
- Traceability Requirement: The rules require messaging platforms to be able to identify the “first originator” of a message, raising privacy concerns.
- Licensing Conditions under Telecom Regulatory Framework:
- Binding Obligations: Requires ISPs to comply with directions issued by the Department of Telecommunications (DoT) and other competent authorities
- Enforcement Mechanism: Non-compliance can lead to penalties, suspension, or cancellation of licenses
- Operational Impact: Ensures that censorship orders are effectively implemented at the network level.
- Example: ISPs blocking specific domains or services following government directives during security situations.
- Confidentiality Clause in Blocking Rules (2009):
- Secrecy of Orders: Mandates strict confidentiality regarding blocking requests and directions.
- Transparency Deficit: Prevents public disclosure of reasons, scope, and number of blocked websites.
- Accountability Constraint: Limits scope for judicial review, public scrutiny, and informed debate.
- Example: Users are often unaware why a particular website is inaccessible, as blocking orders are not publicly available.
Why does censorship vary across ISPs despite identical orders?
- Non-uniform Implementation: ISPs interpret and execute government blocking orders differently based on internal protocols, leading to variation in outcomes.
- Technical Discretion: ISPs choose different blocking techniques such as DNS, HTTP, or TLS filtering depending on their technical setup and preferences.
- Operational Constraints: Variations in infrastructure capacity, technical expertise, and financial resources influence how effectively orders are implemented.
- Compliance Prioritisation: ISPs differ in urgency and strictness while implementing orders, causing delays or partial enforcement.
- Lack of Standardisation: Absence of uniform technical guidelines results in fragmented enforcement across networks.
What technical mechanisms are used for website blocking?
- DNS Blocking: Redirects domain queries to false or incorrect IP addresses through DNS poisoning, preventing access at the resolution stage. Example: Access request to example.com gets redirected to an incorrect or null IP address.
- HTTP Blocking: Restricts access at the application layer by intercepting HTTP requests and returning error or denial responses.
- TLS Blocking: Interferes with encrypted HTTPS connections by blocking or disrupting secure handshakes.
- IP Blocking: Blocks specific IP addresses hosting content, restricting access at the network layer.
- Key Insight: Most Indian ISPs rely primarily on DNS blocking due to its low cost, ease of deployment, and minimal infrastructure requirements.
What does the empirical data reveal about the scale of censorship?
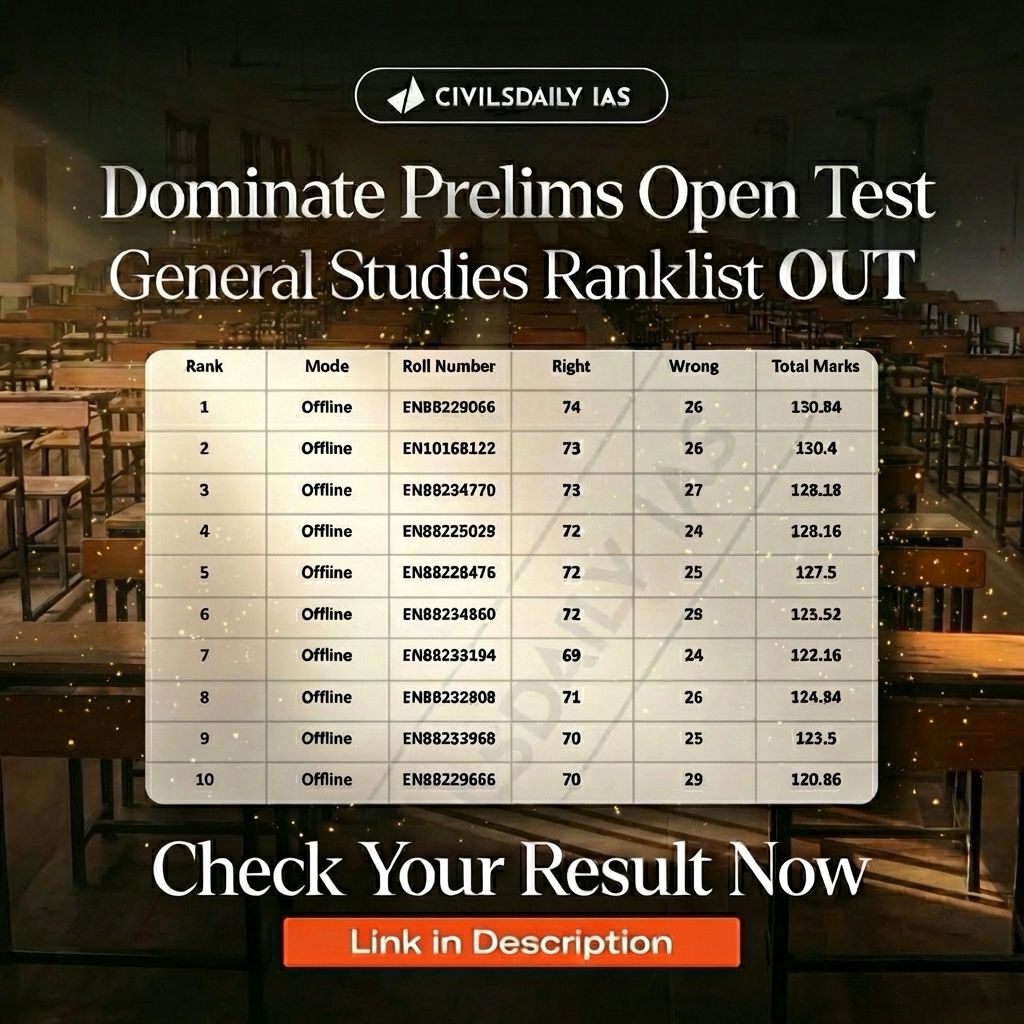
- 294 Million Domains Tested: Large-scale testing conducted across six major ISPs in 2025 to assess censorship patterns.
- 43,083 Domains Blocked: Indicates significant extent of content restriction across networks.
- Only 1,414 Commonly Blocked: Demonstrates that very few domains are uniformly blocked across all ISPs.
- Inter-ISP Variation: Same blocking orders result in different lists of blocked websites across providers.
- Inference: Internet censorship in India operates in a fragmented, inconsistent, and decentralised manner rather than a uniform system.
What are the implications for users and digital rights?
- Unequal Access: Same website may be accessible on one ISP but blocked on another, leading to inconsistent user experience.
- Opacity: Users remain unaware of blocking reasons due to confidentiality of government orders and lack of disclosures.
- Freedom of Expression: Arbitrary and inconsistent restrictions weaken the protection under Article 19(1)(a).
- Accountability Gap: Limited transparency reduces scope for judicial review and public oversight.
- Chilling Effect: Uncertainty about access may discourage users from engaging with certain online content.
Why is DNS blocking problematic as a primary tool?
DNS (Domain Name System) is the “phonebook of the internet,” translating human-friendly domain names (like example.com) into machine-readable IP addresses (like 192.0.2.1). This system allows users to access websites using memorable names instead of complex numerical addresses, acting as a crucial intermediary for web browsers to find and connect to servers.
- Low Precision: Blocks entire domains instead of targeting specific unlawful content, leading to overblocking.
- Circumvention Risk: Easily bypassed using VPNs, proxy servers, or alternative DNS services.
- Security Risks: DNS poisoning may redirect users to malicious or unintended websites, compromising safety.
- Lack of Effectiveness: Ineffective against dynamic or mirror websites that frequently change domains.
- Over-Reliance: Excessive dependence on DNS blocking reflects technological limitations in implementing more precise methods.
Conclusion
India’s internet censorship regime reflects legal backing but weak procedural uniformity and transparency. Addressing these gaps requires standardised implementation, greater accountability, and judicial oversight to balance state interests with fundamental rights.
PYQ Relevance
[UPSC 2013] Discuss Section 66A of IT Act, with reference to its alleged violation of Article 19 of the Constitution.
Linkage: The PYQ Examines limits of state power over online speech under Article 19(1)(a) and safeguards against arbitrary censorship. Similar to Section 66A concerns, the current internet censorship regime (Section 69A, ISP blocking) raises issues of overreach, opacity, and disproportionate restrictions on digital expression.