| PYQ Relevance[UPSC 2023] What are the different elements of cyber security? Keeping in view the challenges in cyber security, examine the extent to which India has successfully developed a comprehensive National Cyber Security Strategy.Linkage: The PYQ directly connects with the article’s themes of cyber threats, legal gaps, attribution challenges, and cyber governance. It helps in linking cyber warfare with India’s preparedness, cyber norms, and accountability mechanisms in internal and international security. |
Mentor’s Comment
The recent Israel-Iran conflict showed that wars are no longer fought only with missiles and soldiers. Along with military attacks, cyberattacks were reportedly used to disrupt websites, communication systems, and digital networks. This has highlighted a growing problem: while cyber warfare is becoming faster and more dangerous, international laws are struggling to hold countries or groups accountable. This is mainly because it is difficult to identify who carried out the attack and prove responsibility.
Why is cyber warfare increasingly becoming an instrument of modern conflict?
- Hybrid Warfare: Combines cyber operations with conventional military action to weaken communication systems, influence public narratives, and disrupt defence preparedness. Recent Israel-Iran tensions reflected simultaneous cyber disruptions alongside kinetic strikes.
- Strategic Disruption: Enables attacks on websites, digital services, and information ecosystems without immediate physical confrontation, reducing costs of escalation.
- Military Utility: Supports conventional military campaigns through disruption of command-and-control systems, logistics, and surveillance capabilities before physical attacks.
- Non-State Participation: Expands battlefield actors beyond states. The pro-Iranian Handala Hack Team reportedly claimed cyberattacks on entities, including a U.S.-based medical technology company.
- Low-Cost Asymmetry: Allows weaker actors to impose disproportionate costs on technologically advanced states through malware, ransomware, or infrastructure sabotage.
Why is establishing legal accountability in cyber warfare so difficult?
- Threshold Ambiguity: International law prohibits the use of force under Article 2(4) of the UN Charter, but determining when cyber operations amount to “use of force” remains contested.
- Classification Problem: Distinguishing between cyber espionage, cybercrime, sabotage, and armed attack remains legally unclear, complicating state responsibility.
- Attribution Challenge: Cyber operations are covert by nature. Attackers frequently conceal origins through proxy servers, spoofing, and third-party infrastructure, making definitive attribution difficult.
- State Responsibility Gap: International law requires attribution of conduct to a state for legal responsibility. Technical suspicion often fails to meet evidentiary thresholds admissible before courts.
- Uncertain Harm Assessment: Difficulty in proving direct causation between cyber operations and measurable physical or economic harm weakens accountability.
- Example: Cyberattacks targeting critical infrastructure may create large-scale disruption, yet legal consequences remain limited if attribution cannot be conclusively established.
How do limitations of international law weaken cyber accountability?
- Legal Applicability: Existing principles of sovereignty, non-intervention, and prohibition of force theoretically apply to cyberspace.
- Enforcement Deficit: International legal frameworks rarely produce prosecutions or compensation despite growing cyber incidents.
- Doctrinal Mismatch: Traditional legal frameworks were developed for geographically identifiable and physically attributable conflict, unlike decentralized cyber operations.
- Absence of Consensus: States disagree on what constitutes armed attack, proportionality, and lawful retaliation in cyberspace.
- Normative Fragmentation: Different national interpretations prevent development of universally accepted cyber rules.
- Example: A cyberattack disrupting electricity or healthcare systems may create severe consequences but still fall into a legal grey zone below the threshold of armed conflict.
Why do attribution and evidence create major barriers to litigation?
- Secrecy of Operations: Cyber incidents frequently involve classified intelligence, covert capabilities, and anonymous actors.
- Evidentiary Constraints: Technical evidence often remains insufficient for legal admissibility in courts.
- Causation Complexity: Courts face difficulties in establishing who conducted the operation, the extent of damage caused, and links to specific harm.
- Sensitive Information Risks: Litigation may require disclosure of intelligence capabilities, creating national security concerns.
- Escalation Risks: States often avoid formal legal proceedings to prevent diplomatic retaliation or military escalation.
- Example: Even where intelligence agencies possess strong suspicions, states may avoid public attribution due to inability to disclose classified evidence.
Why are international legal forums inadequate for cyber disputes?
- Jurisdictional Limitations: The International Court of Justice (ICJ) requires state consent, limiting compulsory dispute settlement.
- Sovereign Immunity: Foreign states often enjoy immunity protections in domestic courts.
- Institutional Deficit: No dedicated global tribunal exists for cyber conflict resolution.
- Cross-Border Complexity: Cyber operations transcend territorial boundaries, complicating jurisdiction.
- Limited Legal Remedies: Victims struggle to secure reparations, injunctions, or punitive action.
- Example: Domestic courts face obstacles when foreign-state actors conduct cyber intrusions through multiple jurisdictions.
How are international institutions attempting to regulate cyberspace?
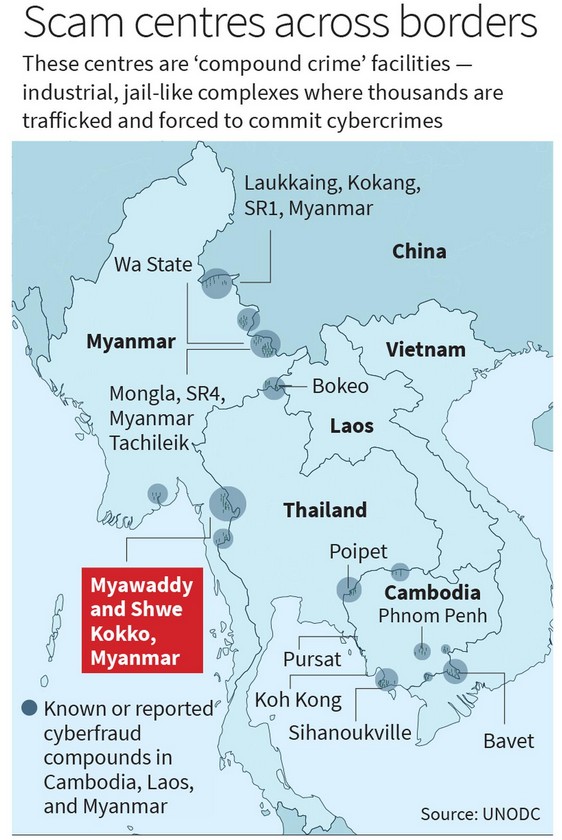
- Budapest Convention on Cybercrime: Establishes international cooperation mechanisms against cybercrime and digital evidence sharing. However, focus remains primarily on criminal enforcement rather than state cyber warfare.
- UN Convention against Cybercrime: Expands global legal cooperation to address emerging cyber threats.
- UN Framework Discussions: Ongoing deliberations seek responsible state behaviour, accountability norms, and confidence-building measures in cyberspace.
- Norm Development: Attempts to define acceptable conduct, critical infrastructure protection, and proportional responses.
- Implementation Gap: Enforcement mechanisms remain weak despite institutional developments.
Why must India actively shape emerging cyber norms?
- Digital Dependence: India increasingly relies on digital infrastructure across finance, governance, energy, healthcare, and defence.
- Strategic Vulnerability: Greater digitisation increases exposure to cyber espionage, infrastructure disruption, and information warfare.
- Normative Leadership: India can influence evolving global cyber governance frameworks through multilateral diplomacy.
- Institutional Participation: Active engagement in accountability, attribution standards, and responsible state behaviour strengthens India’s strategic interests.
- Cyber Preparedness: Enhances resilience of critical information infrastructure and national security architecture.
- Example: India’s expanding digital public infrastructure, including UPI and Aadhaar-linked systems, requires stronger cyber resilience frameworks.
Conclusion
Cyber warfare is growing faster than global laws can handle. It is difficult to identify attackers and prove responsibility. Existing legal systems are not fully prepared for digital conflicts. Countries, including India, must strengthen cyber security and help build stronger global cyber rules.
International Legal Frameworks Relevant to Cyber Warfare
- Tallinn Manual 2.0: Non-binding academic interpretation of how international law applies to cyber operations and cyber warfare.
- Article 2(4), UN Charter: Prohibits threat or use of force against territorial integrity or political independence of states.
- Due Diligence Principle: The concept was solidified by the International Court of Justice (ICJ) in the landmark 1949 Corfu Channel Case, which ruled that a state cannot knowingly allow its territory to be used for acts contrary to the rights of other states.
- Principle of Sovereignty: Recognises cyber intrusions into critical systems as possible violations of territorial sovereignty. It is anchored in the UN Charter (1945) under Article 2(1), which declares the sovereign equality of all member nations.
- Law of Armed Conflict (LOAC): Governs proportionality, distinction, and military necessity in cyber-enabled warfare. It is heavily codified under the Geneva Conventions of 1949 and their Additional Protocols (1977), as well as the Hague Conventions. It is also known as International Humanitarian Law (IHL).
India’s Cyber Institutional Architecture
- CERT-In: Coordinates cyber incident response and vulnerability management.
- National Critical Information Infrastructure Protection Centre (NCIIPC): Protects critical sectors including banking, telecom, power, and transport.
- National Cyber Security Policy: Strengthens resilience, skill development, and institutional coordination.
- Indian Cyber Crime Coordination Centre (I4C): Supports cybercrime prevention and inter-agency cooperation.

































 Context
Context  Status of cyber investigation
Status of cyber investigation



